I’m struggling to securely connect to our manufacturing network from offsite locations. There are strict compliance standards to consider, and I want to avoid any vulnerabilities. Has anyone dealt with this or can offer tips on the best secure remote access solutions for manufacturing environments?
Hey, all—
So, I’ve spent a fair chunk of time sorting out remote access solutions in industrial settings, and honestly, the security headaches never seem to let up. For anyone else facing the “how do I let outside support in without opening Pandora’s box?” conundrum, here’s a no-BS comparison of three options I’ve personally kicked the tires on lately: HelpWire, TeamViewer, and BeyondTrust.
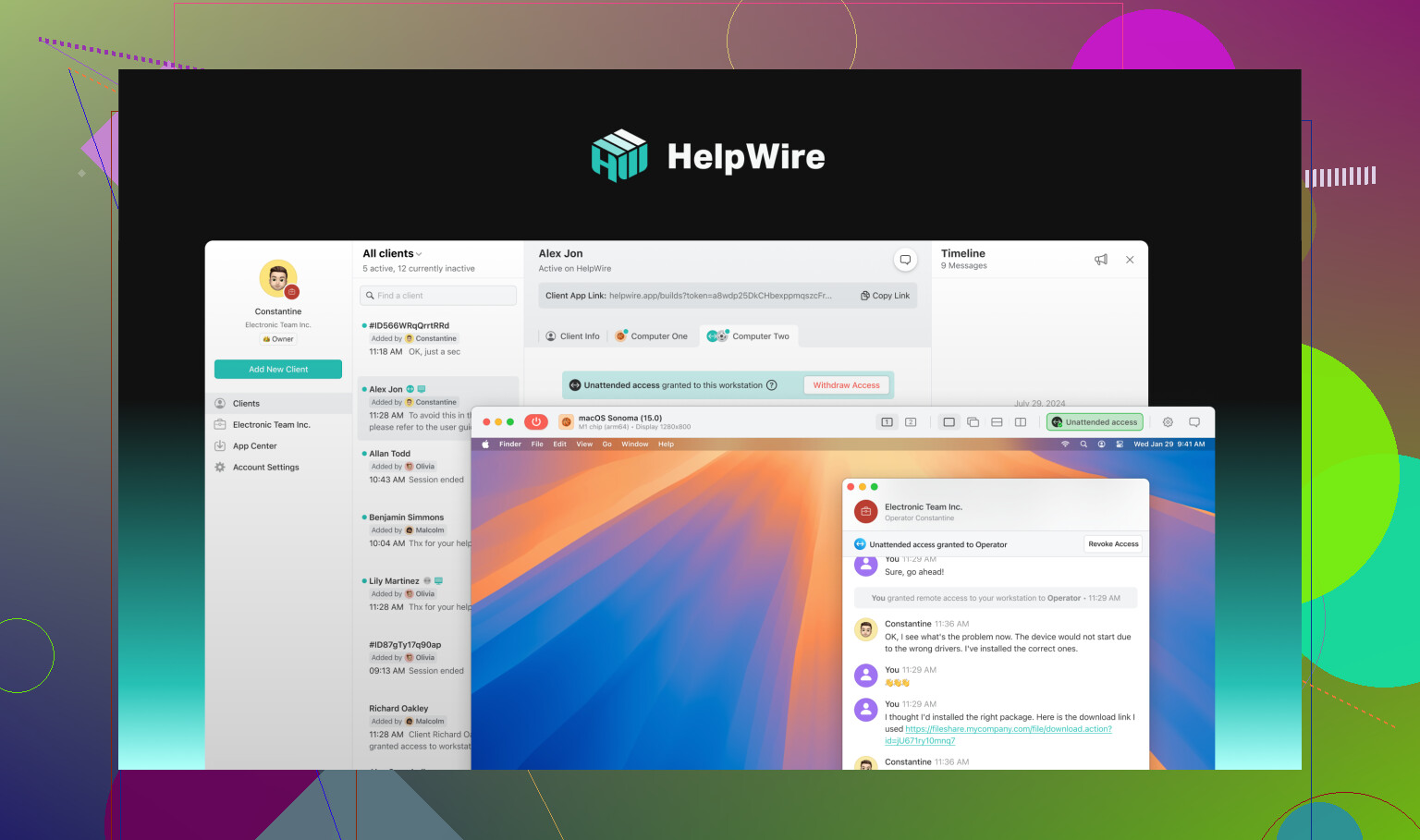
HelpWire: The No-Fuss Lightweight Shield
Ever use a tool that feels like flipping on a flashlight in the dark? That’s HelpWire for me—super simple, totally free, and (surprisingly) takes security pretty seriously. The devs seem obsessed with safety over frills, and you can check their security docs if you’re paranoid, like me. Especially for manufacturing environments, it checks a lot of boxes:
-
Encryption That’d Make the NSA Sweat
They go hard with AES-256 plus TLS/SSL. Basically, if someone’s eavesdropping, they’ll just hear static. -
Peer-to-Peer Default
Most connections happen directly between endpoints—bye-bye, random relay servers eating your secrets for breakfast. -
AWS Backup When Direct Won’t Work
Sometimes strict networks choke P2P, so they’ll route stuff through beefy AWS servers (using anonymized traffic). -
Legit Auth
Auth0 handles logins, and every build’s signed by DigiCert. Spoofers? Take a hike. -
Built for the Shop Floor
You can use it on Windows, Mac, or Linux, and it doesn’t freak out with unattended or spur-of-the-moment support in industrial chaos.
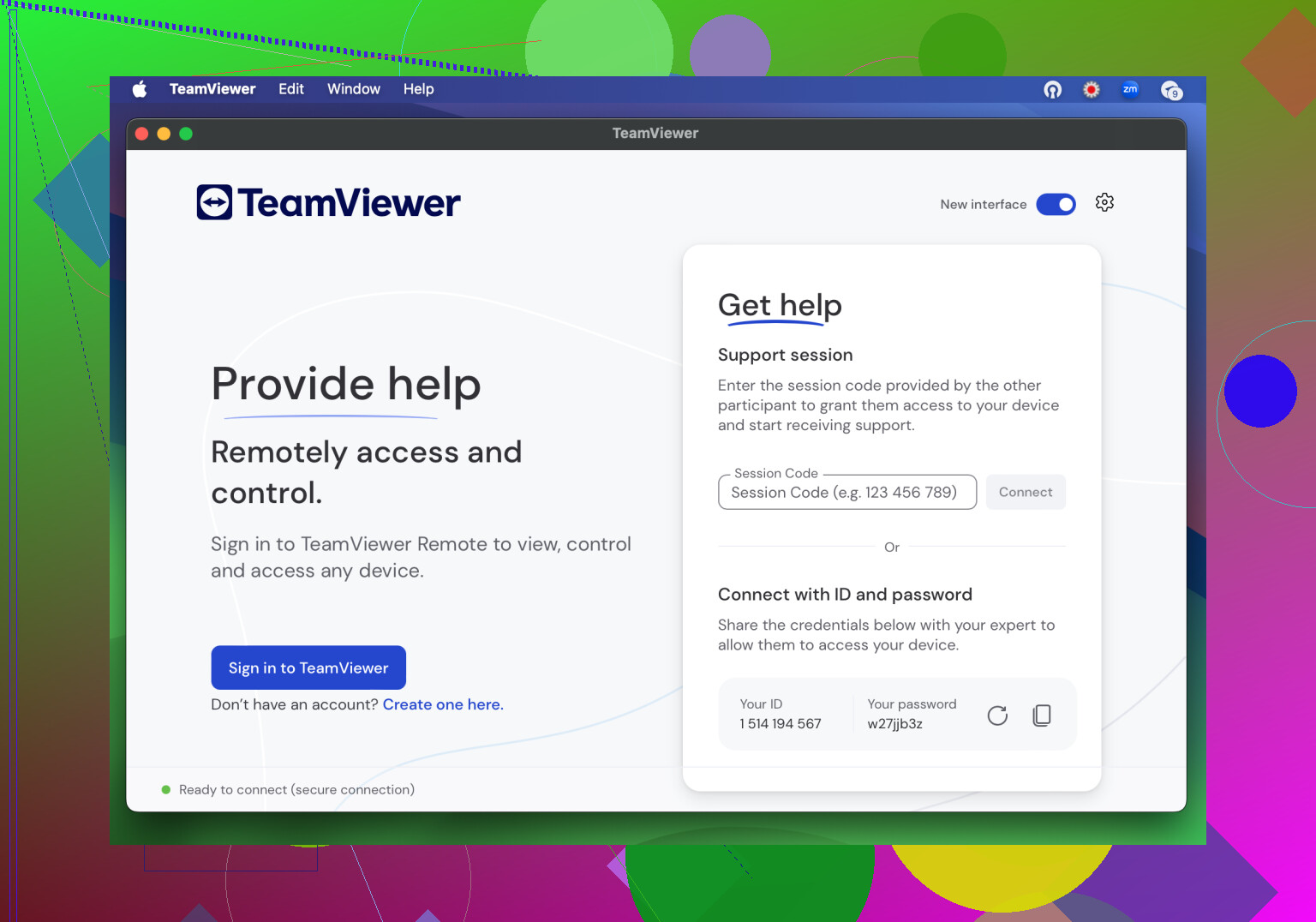
TeamViewer: Old Guard with Steel Doors (Mostly)
Everyone’s heard of TeamViewer—even my grandma’s IT guy uses it. When it comes to security, this thing is loaded up like an armored truck. But before you get too comfy, note their 2024 run-in with APT29 (more later).
-
Superhuman-Level Encryption
AES-256 end-to-end, RSA 4096 for key exchange, all with TLS tunnels. Even if you’re windsurfing suspicious networks, your session shouldn’t leak. -
Layered Logins Galore
TeamViewer Tensor lets you do SSO, 2FA, and granular conditional access—a Field of Dreams for compliance nerds. -
Can Tunnel Like a Mole
If your firewall is built like Fort Knox, it’ll drop to HTTP tunnels to make sure remote work doesn’t stop. -
Recent Breach (Not You, But Still…)
So, yeah—summer 2024, their parent company got slammed by a nation-state actor. TeamViewer swears clients weren’t hit and their core product stayed clean, but still. Make of that what you will.
BeyondTrust: Control Freak’s Dream (With Baggage)
Let’s be real—if you need 24/7 logs, vaulting, access approval, and so many authentication steps you lose count, BeyondTrust is what the compliance gods would ask for. Not just remote support: full-on privileged access management.
-
Always Goes Military-Grade
Everything’s encrypted, TLS 1.2 everywhere, and you get the option for custom key management and even encrypting data at rest. -
Fine-Grained Permissions for Days
This is for the folks running nuclear plants or pharma labs: credential vaults, password masking/rotation, SSO, layered MFA, real-time approvals, and audit logs so detailed your ISO auditor will weep with joy. -
Drama in High Places
Heads-up: a breach in 2024 involved someone grabbing BeyondTrust API keys and busting into US Treasury systems. It wasn’t a software bug, but it’s a reminder—remote access in high-value setups is always a double-edged sword.
TL;DR
If you’re running industrial stuff and only want what’s safe for manufacturing secure remote access, HelpWire is the new kid with surprisingly tough locks, TeamViewer is the old reliable (recently spooked, but still sturdy), and BeyondTrust is straight-up designed for control-freak admin types with a taste for drama. Each has its skeletons, so pick your poison.
Alright, I’ll be honest—remote access for manufacturing is like setting up a guard dog that sometimes bites its owner. I’ve danced this compliance-vulnerability tango, and while options like the ones @mikeappsreviewer lists (handy rundown btw) all do the job, sometimes less is more.
First off, fancy tools are great, but don’t kid yourself: your #1 vulnerability is sloppy network segmentation. I see too many folks slap a remote access solution on the same subnet as PLCs, MES, IoT junk—nightmare fuel. Start with professional-grade firewalls, strict VLAN separation, and segment off anything critical. If you don’t have jump servers/bastion hosts for remote entry—set them up. Lateral movement is the devil.
Also, traditional VPNs? They’re everywhere, but “secure” is only as strong as your weakest user’s password. If you MUST use VPNs, go with always-on 2FA/MFA, time-based access, and throw your audit logs someplace offsite. Compliance likes audit trails, but it loves immutable storage even more.
@Mikeappsreviewer likes HelpWire (and honestly, lightweight tools are GREAT in lean shops), but I gotta nitpick: simplicity is good, but make sure you overlay it with your own logging/SIEM for that compliance report. Out-of-the-box logs often don’t cut it when the auditors come hunting.
Zero trust remote access tools—think newer-gen (look up Cloudflare Access, ZScaler Private Access)—can add a layer, especially if you’re averse to VPN holes poked in your castle walls. These let you say “this user can access this device/service for 20 mins, period” and nothing else.
Also, NO tool saves you from old firmware on devices. Patch your edge gear, and run pen tests BEFORE you roll out remote access to vendors or your own OT team. And to spice it up—if you haven’t run a tabletop exercise for “what if remote access gets hijacked,” do one. It’ll terrify your C-suite and fix holes fast.
Bottom line? Don’t trust anything by default. Tools help, but architecture, process, and paranoia will take you further than cutting-edge software alone. And, hey, if you only let in remote access during emergencies or with hand-holding via HelpWire or similar, that’s not a bad move either.
Here’s the thing—secure remote access in manufacturing isn’t just a tech problem, it’s a people (and process) problem too. Everyone’s out here throwing products at the wall (HelpWire, TeamViewer, BeyondTrust, yadda yadda) but if your internal policies and user discipline are trash, none of these will save your bacon.
Let’s cut through it: firewalls and VLANs are your first line, not the remote tool. Make your remote access endpoints a black hole to anything but approved IPs and ports, and for the love of Bob, restrict accounts to minimum needed privileges. Yes, audit everything, and yeah, immutable logs are nice, but don’t just rely on the compliance checkbox—real-time monitoring is how you catch the “oops” before it becomes a headline.
I agree with the previous posters on not using VPNs willy-nilly. But, Zero-Trust isn’t magic fairy dust either—those Cloudflare and ZScaler ZTNA thingies demand their own discipline and can be a bear to integrate with creaky factory kit (Siemens S7 anyone?). Sometimes your legacy gear just won’t play nice.
If you want no-nonsense, HelpWire is the “it just works” tool out of the ones mentioned. Its P2P design and strict encryption actually make sense for most SMB manufacturing outfits who don’t have armies of IT staff. But, don’t let the “simple” tag lull you—still gotta pipe those logs to your SIEM and run drills for account compromise. (And yes, I know some auditors look at you funny if the remote solution has a free tier, but so what, they’ll live.)
One last missile: Patch. Your. Edge. Devices. Factory floor endpoints are sitting ducks. Remote tools are a risk multiplier, not a magic shield.
So, in summary, tools matter, but architecture, user discipline, and a fat dose of skepticism matter more. And sometimes the best route is “no remote by default, temporary, logged, and supervised when absolutely needed.” This approach freaks out impatient vendors, but it will let you sleep at night.